Blog
Thought leadership and expert perspectives from the Trulight team.

Expect the Unexpected
SolarWinds went undetected for nine months. The breach that keeps a CIO awake isn't the one in the headlines — it's the one nobody knows about yet. Building resilience for the unknown.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
Cyber in a Hurricane
While organizations scramble to recover from natural disasters, cyber criminals see opportunity. How to maintain security discipline when everything around you is in chaos.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
Unexpected
From business email compromise to supply chain infiltration, the most dangerous attacks are the ones you don't see coming. A multi-layered approach to defending against the unexpected.
 Jonathan Kilpatrick
Jonathan Kilpatrick 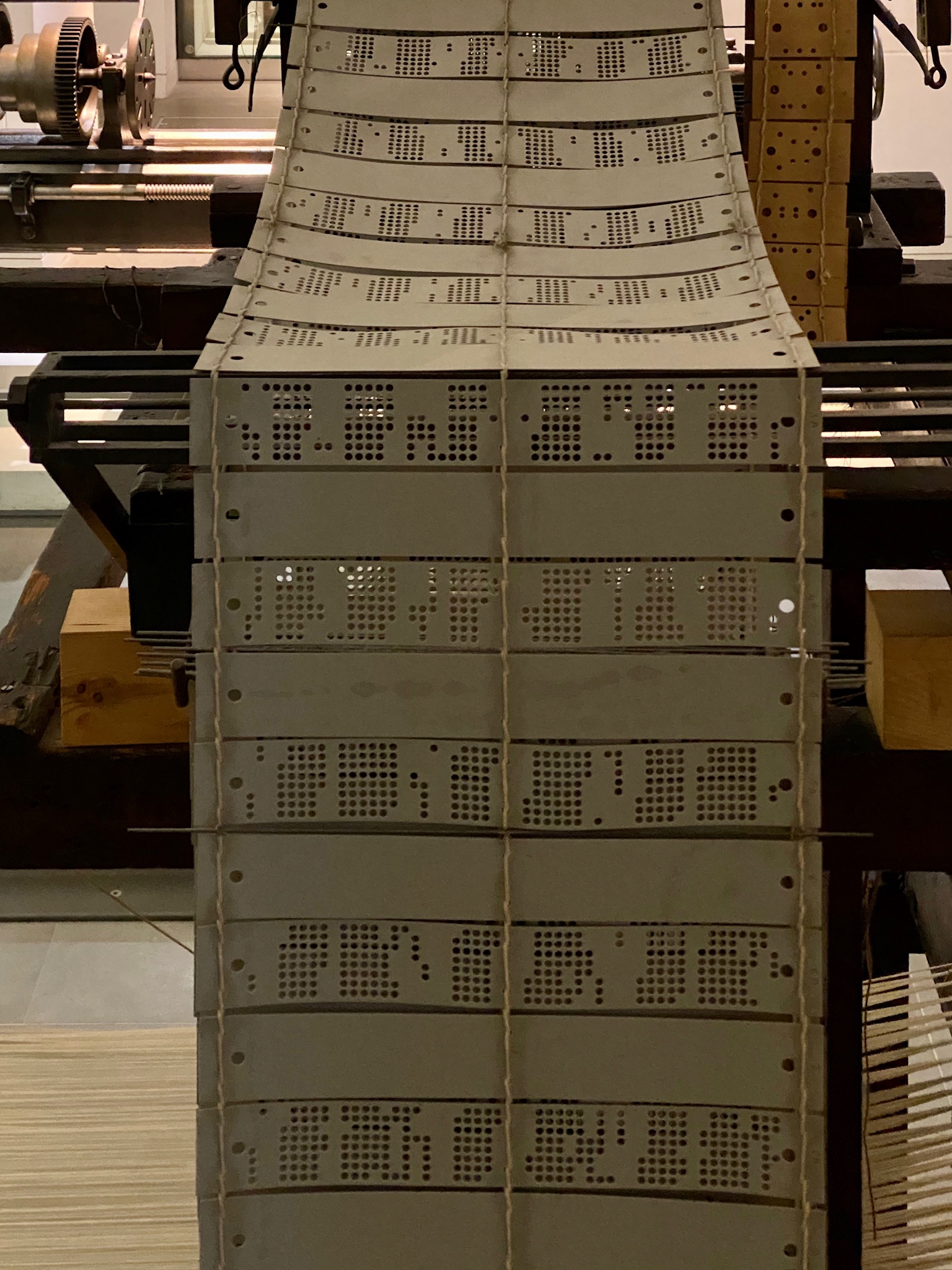
First Cyber Hack
The world's first cyber attack happened in 1834 — two brothers hacking a mechanical telegraph for insider trading. The technology has changed; human greed hasn't.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
No such thing as Stress
A professor once said: stress is a made-up word — it's really low-grade fear. Once you name the fear, you can do something about it. A framework for leaders and organizations alike.
 Jonathan Kilpatrick
Jonathan Kilpatrick 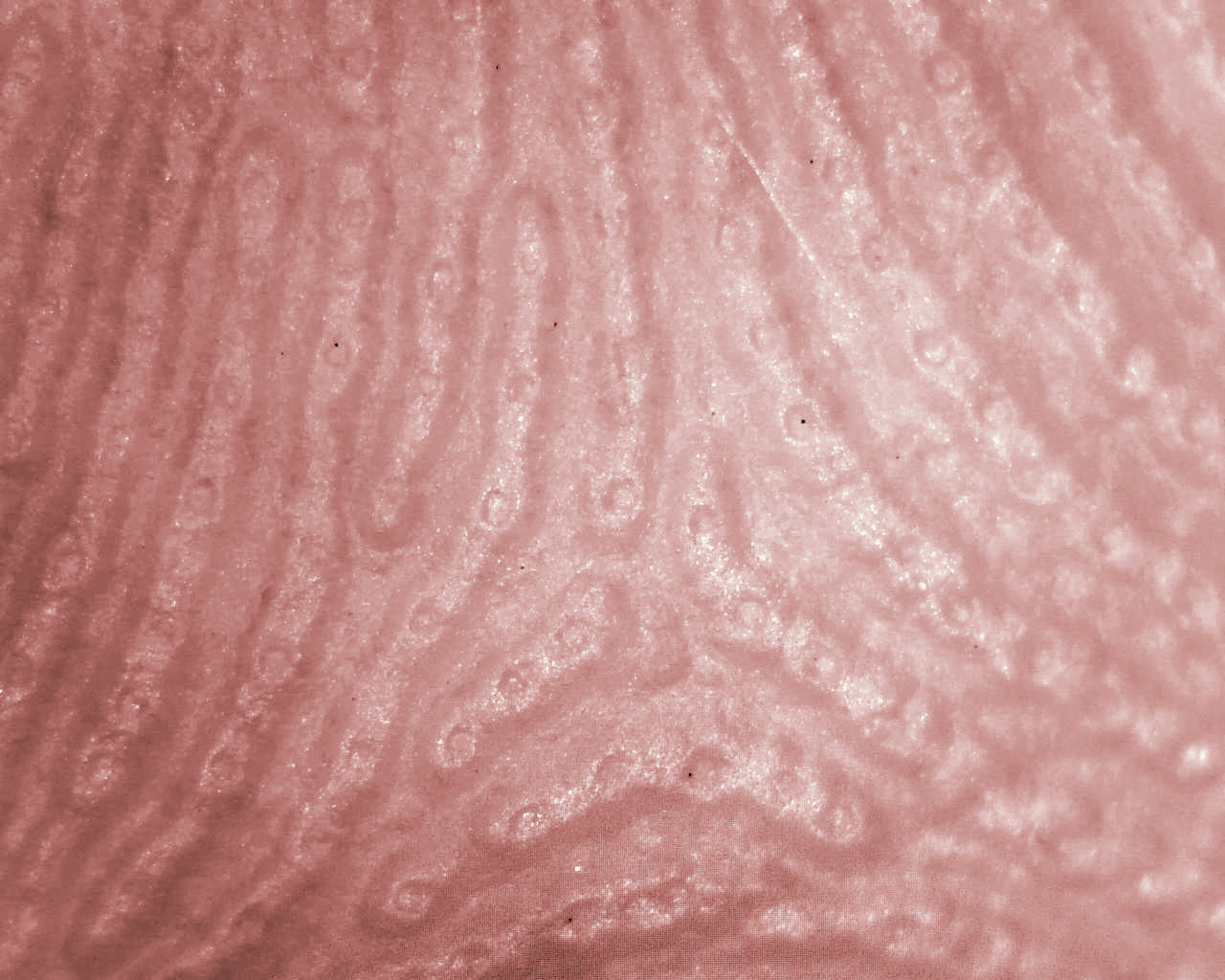
You are Unique
Every organization claims to be different — but do you know how? An honest SWOT analysis reveals the strengths that set you apart and the weaknesses that leave you exposed.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
Active Cyber Defense
NIST defines active cyber defense as real-time capability to discover, detect, and mitigate threats. Like taking your vitamins, proactive defense means thinking like an attacker before one strikes.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
Sensible Cyber Security
88% of U.S. businesses have fewer than 20 employees — and most lack a dedicated security team. Here are practical, budget-friendly steps any small business can take to reduce cyber risk.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
Open Source
Over 75% of organizations rely on open-source software — but many don't vet it for vulnerabilities. If you're not scanning and updating third-party code, attackers are watching for your oversight.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
Unknown Threat
The known threats don't keep a CIO awake at night — it's the breach you haven't heard about yet. How to prepare for zero-day vulnerabilities and the attacks that haven't made the news.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
SolarWinds Again
Three new SolarWinds vulnerabilities disclosed — including one that decrypts the Orion database password in a single line of code. Patches are available; here's what you need to know.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
CJIS
CJIS compliance is essential for the 18,000+ law enforcement agencies that access the FBI's criminal justice database — and it's not easy to attain. Understanding the requirements and your options.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
SUDO Vulnerability
A decade-old vulnerability in sudo — found on nearly every Linux system, IBM AIX, and macOS — lets any user gain root privileges without credentials. Patch now before it's exploited.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
Strategy
A sound technology strategy maximizes opportunity and minimizes risk. Learn why knowing your organization's strengths — and its limitations — is the foundation for sustainable success.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
Cyber Security In Pandemic
Cyber criminals won't pause for a pandemic. With up to 40% of the workforce displaced, remote access surging, and security teams stretched thin, your organization needs a plan before crisis hits.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
Does Your Computer Read the Newspaper?
Critical vulnerabilities make headlines every week, but your servers can't read the news. Staying current on threat assessments and patching promptly is the simplest way to harden your defenses.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
Full Contact Chess
Effective cyber security requires both strategy and muscle — firewalls alone aren't enough, and brute-force response without a plan is even worse. Does your organization have both?
 Jonathan Kilpatrick
Jonathan Kilpatrick 
Why Oldsmar??
When hackers targeted a small Florida water utility, the deeper question wasn't just who — it was why. The Oldsmar attack may have been a dry run for something much larger.
 Jonathan Kilpatrick
Jonathan Kilpatrick 
Technology Touches Everything
Technology has evolved from a back-office support function into a full partner in every business decision. So why don't most technology leaders have a seat at the table?
 Jonathan Kilpatrick
Jonathan Kilpatrick 
SolarWinds
If FireEye and Microsoft fell to the SolarWinds breach, every organization is vulnerable. Immediate steps and long-term strategies to protect your systems in the aftermath.
 Jonathan Kilpatrick
Jonathan Kilpatrick